
It is a every day process for many Linux customers, but it could be baffling for someone who's got nonetheless to test it. This short article describes tips on how to configure two desktops for secure shell (SSH) connections, and how to securely connect from a single to another and not using a password.
SSH keys are by default held in the ~/.ssh Listing. If you do not Use a ~/.ssh Listing, the ssh-keygen command produces it in your case with the correct permissions. An SSH essential is created being a resource and saved in Azure for afterwards use.
Every time you need to do SSH, the RSA key to the SSH relationship for respective hostname is stored inside of ~/.ssh/known_hosts file
PuTTY does not preserve the general public important for you personally. You can copy and paste it on to your authorized_keys file or duplicate and paste this key into a notepad doc for Harmless maintaining to copy later on.
V2Ray DNS tunneling is usually a approach to transporting arbitrary networking facts over an encrypted V2Ray DNS link. It can be employed to add encryption to legacy programs. It can also be accustomed to carry out VPNs (Virtual Private Networks) and entry intranet products and services across firewalls. V2Ray DNS is a typical for safe distant logins and file transfers around untrusted networks.
Quite a few present day typical-function CPUs even have components random number generators. This helps quite a bit with this problem. The ideal exercise is to collect some entropy in other means, even now keep it in a very random seed file, and mix in certain entropy in the components random number generator.
* If utilizing PuTTY the public key is shown in the window and never within a independent file. See stage 4 of "Generating SSH keys with PuTTY" above. That would be the critical wanted in your Slash and paste. ↩ Again
On the other hand, OpenSSH certificates can be quite valuable for server authentication and might obtain related benefits since the normal X.509 certificates. Nevertheless, they require their very own infrastructure for certification issuance.
You now Have got a public and private SSH critical pair You should utilize to entry distant servers and to handle authentication for command line packages like Git.
When you're prompted to "Enter a file through which to save lots of The true secret", you could push Enter to accept the default file spot. Be sure to Be aware that when you produced SSH keys Earlier, ssh-keygen may perhaps inquire you to rewrite A further important, through which circumstance we recommend making a personalized-named SSH vital. To do so, kind the default file spot and replace id_ALGORITHM together with your tailor made key title.
Get InvolvedJoin us on our mission to safe on line encounters for all. Turn into a CIS member, partner, or volunteer—and investigate our vocation possibilities.
If you enter a single, It's important to provide it each and every time you employ this critical (unless createssh you're working SSH agent software package that suppliers the decrypted key). We suggest utilizing a passphrase, however you can press ENTER to bypass this prompt.
Once you've checked for present SSH keys, you can create a different SSH vital to make use of for authentication, then incorporate it to your ssh-agent.
You'll be able to spot the public crucial on any server then connect with the server employing ssh. If the public and private keys match up, createssh the SSH server grants accessibility without the require for any password.
 Jake Lloyd Then & Now!
Jake Lloyd Then & Now! Kel Mitchell Then & Now!
Kel Mitchell Then & Now!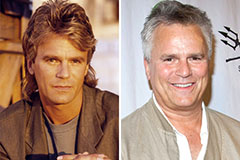 Richard Dean Anderson Then & Now!
Richard Dean Anderson Then & Now! Terry Farrell Then & Now!
Terry Farrell Then & Now! Rossy de Palma Then & Now!
Rossy de Palma Then & Now!